NETinVM
Exercise: Capturing an HTTP session with Wireshark
| Authors: | Carlos Perez |
|---|---|
| Date: | 2025-09-05 |
Objective
The goal of this exercise is to capture an HTTP session using Wireshark, thus showing how NETinVM can be used for teaching and learning.
Introduction
As an example of how NETinVM can be used for teaching and learning, this section will show how the network traffic of an HTTP connection could be generated, captured and analyzed within NETinVM Wireshark.
Once all virtual systems have been started within NETinVM by executing the 'netinvm_run_all' shell script, the procedure to follow is just as simple as if all systems were real. We will establish an HTTP connection from 'exta' to 'www.example.net' and we will capture and analyze that traffic using 'wireshark' running on 'base'.
Note
Note that 'base' has access both to the external network ('ext') and the screened subnet ('dmz') through its 'virbr-ext' and 'virbr-dmz' network interfaces, respectively. However, in order to be able to capture all the network traffic, each switch has a mirror port, named after its network ('mirror-ext' and 'mirror-dmz'). Thus, we will be able to capture the traffic on either network (or on both at the same time) since packets will travel from 'exta' to 'fw' through the external network and then from 'fw' to 'www.example.net' ('dmza') through the 'dmz' network, and back. For this exercise, we will assume that we are interested only in the traffic in the 'dmz' network, so mirror port 'mirror-dmz' will be used.
Preparation
In order to perform the exercise the NETinVM environment must be brought to life by peforming the following actions:
Start the VMware virtual machine "NETinVM"
Start, inside "NETinVM", the KVM (Kernel Virtual Machines) virtual machines by running in "base", as user "user1", the command "netinvm_run_all" (or else, use the "Run all" button).
Log in as "root" in "exta"
Verify there is network connectivity between "exta" and "dmza" by running in "exta", as user "root", the following command:
root@exta:~# ping -c 1 dmza PING dmza.example.net (10.5.1.10) 56(84) bytes of data. 64 bytes from dmza.example.net (10.5.1.10): icmp_seq=1 ttl=63 time=2.67 ms --- dmza.example.net ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 2.677/2.677/2.677/0.000 ms root@exta:~#
If the number of packets transmitted and received is the same, as shown above ("1 packets transmitted, 1 received"), everything is working fine. If, on the contrary, no response from the target system is received then there is some kind of problem that will need to be resolved before continuing with the excercise.
HTTP session capture
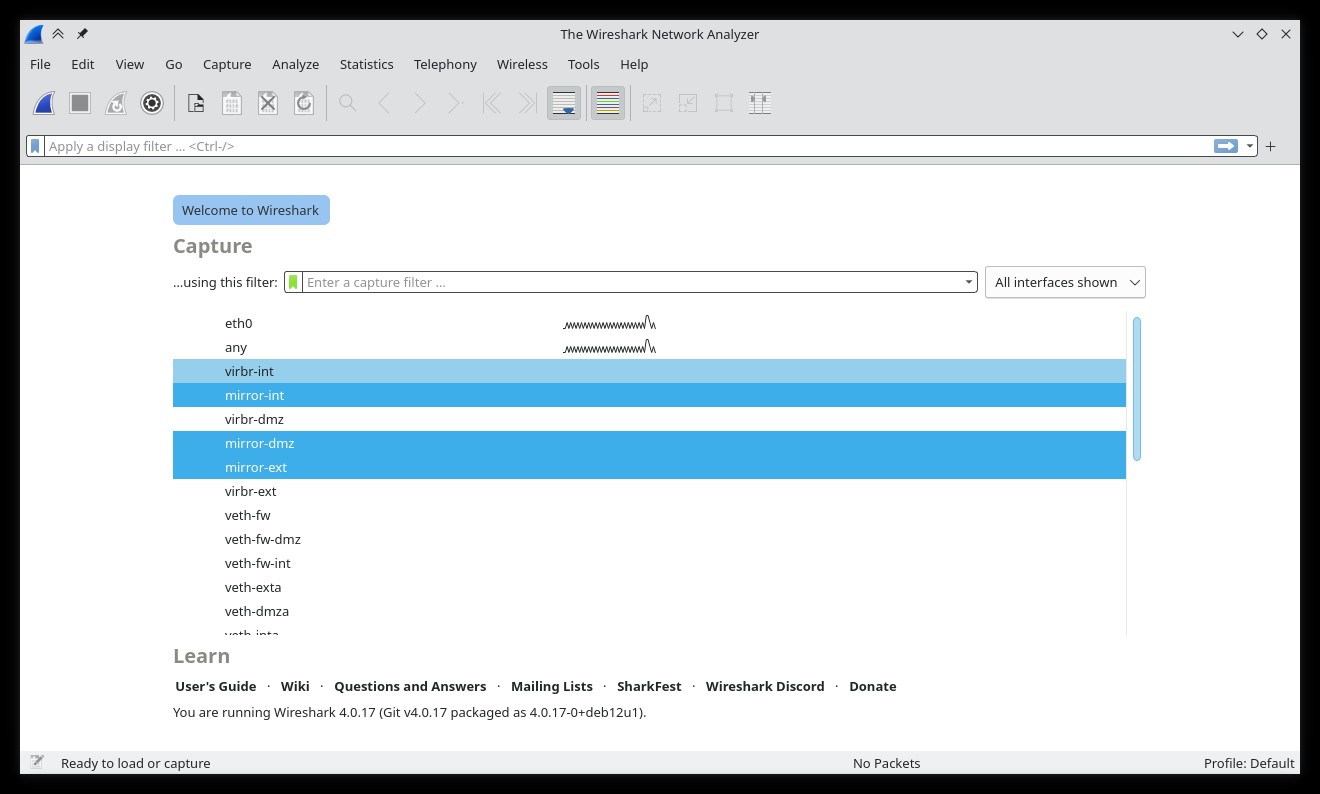
First, start 'wireshark' on 'base' and set it to listen on the 'dmz' network (interface 'mirror-dmz')
Then, request the home page of the web server running on 'www.example.net' by executing the following command in "exta":
root@exta:~# wget www.example.net
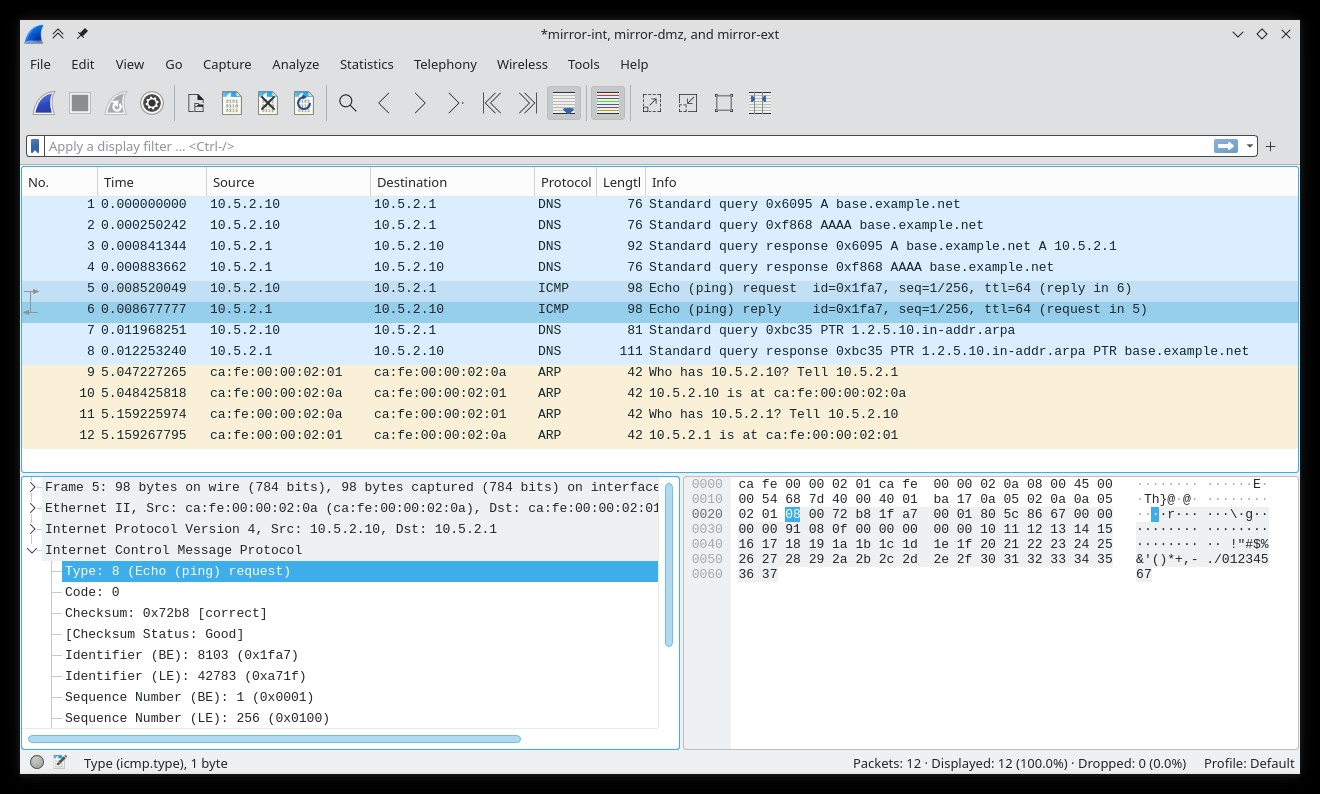
Finally, go back to 'wireshark', stop the capture and analyze the traffic at your leisure. The session captured in 'wireshark' will look similar to the following figure, which shows the HTTP session that was established between 'exta' (10.5.0.10) and 'www.example.net' (dmza, 10.5.1.10)